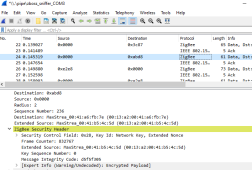
Seems to be 128 bit AES with no integrity protection, at least in that setting it shows transport keys when used with the default center key (i.e., 5a6967426565416c6c69616e63653039). Most of what I've seen online has 32 bit integrity protection, so quite possibly this is wrong. Also, entering the first key does not automatically transpose the other keys (although, each device might have its own key).
(With no integrity protection, in one of the "unknown Commands", is a "Key ID: Key-load key").
JSON is nice in that it has a key-value pair, for example ["kwh", "12"]. That is looking at the key gives you some context as to what the value means.
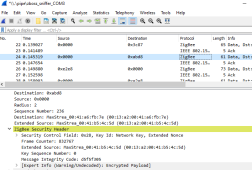
Zigbee is not like this. Zigbee uses "Zigbee Cluster Libraries" (
ZCL) to provide the context, instead of transmitting a string of the context a data value is supplied. There are a lot of ZCLs and different packets can reference different ones. For example, a SensorTag might be On/Off, Temperature Measurement.
When the library is public (published?) it is probably relatively easy to parse what's going on. What I'm seeing a lot of is "ZCL: Unknown Command". Assuming I have the correct network keys and integrity protection that is. There are manufacturer's codes for the ZCLs, so it might be possible they publish them, something to follow up on.
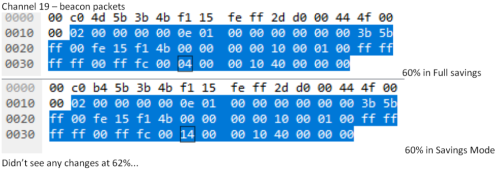
If not, it might be possible to deduce them with a controlled capture with the system at different operational conditions. A quick scan by packet size shows probably less than 50 types of messages, but still a monumental task.